| 1 |
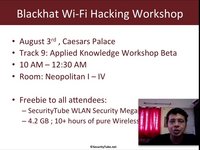 |
Securitytube Blackhat And Defcon Workshops Announcement |
13 years |
Vivek-Ramachandran |
blackhat, defcon, workshop, announcement |
8846 |
9 |
| 2 |
 |
Defcon 18: How To Hack Millions Of Routers 1/3 |
13 years |
rootx |
routers, defcon, hacking |
9832 |
None |
| 3 |
 |
Defcon 18: How To Hack Millions Of Routers 2/3 |
13 years |
rootx |
routers, defcon |
5452 |
None |
| 4 |
 |
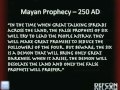
Defcon 18: How To Hack Millions Of Routers 3/3 |
13 years |
rootx |
routers, defcon |
6068 |
None |
| 5 |
 |
Securitytube Live: Defcon 19 And Blackhat Coverage |
12 years, 12 months |
SecurityTube_Bot |
securityube, live, defcon, blackhat |
6975 |
20 |
| 6 |
 |
Ripping Media Off The Wire (Defcon 18) |
12 years, 11 months |
SecurityTube_Bot |
defcon, media, talk |
4916 |
None |
| 7 |
 |
Steal Everything, Kill Everyone, Cause Total Financial Ruin! (Or How I Walked In And Misbehaved) |
12 years, 11 months |
SecurityTube_Bot |
jason, street, defcon, 19 |
6361 |
3 |
| 8 |
 |
A Distributed Preservation Of Service Attack |
12 years, 10 months |
SecurityTube_Bot |
defcon, 19, textfiles |
4529 |
None |
| 9 |
 |
Defcon 17: Advanced Mysql Exploitation |
12 years, 9 months |
Insecurestuff |
Mysql, defcon, penetration testing |
7101 |
None |
| 10 |
 |
Defcon 19: Making Of The Badge |
12 years, 4 months |
SecurityTube_Bot |
securitytube, defcon, def con, hacking, hackers, information security, hacking, convention, computer security, DC 19, Defcon 19, dc-19 |
8651 |
None |
| 11 |
 |
Defcon 19: The Future Of Cybertravel: Legal Implications Of The Evasion Of Geolocation |
12 years, 4 months |
SecurityTube_Bot |
defcon 19, defcon |
3588 |
2 |
| 12 |
 |
Defcon 19 - Fix It In Software |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
8259 |
1 |
| 13 |
 |
Defcon 19 - When Space Elephants Attack: A Defcon Challenge For Database Geeks |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7908 |
None |
| 14 |
 |
Defcon 19 - Bosses Love Excel, Hackers Too. |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
10642 |
None |
| 15 |
 |
Defcon 19 - Dust: Your Feed Rss Belongs To You! Avoid Censorship |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7402 |
None |
| 16 |
 |
Defcon 19 - Ip4 Truth: The Ipocalypse Is A Lie |
12 years, 4 months |
Securitytube_Poster |
Securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
8076 |
None |
| 17 |
 |
Defcon 19 - Security When Nano Seconds Count |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6962 |
None |
| 18 |
 |
Defcon 19 - Beat To 1337: Creating A Successful University Cyber Defense Organization |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7490 |
None |
| 19 |
 |
Defcon 19 - Pillaging Dvcs Repos For Fun And Profit |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7043 |
None |
| 20 |
 |
Defcon 19 - Chip And Pin Is Definitely Broken |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7265 |
None |
| 21 |
 |
Defcon 19 - Deceptive Hacking: How Misdirection Can Be Used To Steal Information Without Being Detected |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
8220 |
None |
| 22 |
 |
Defcon 19 - Fingerbank - Open Dhcp Fingerprints Database |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
9704 |
None |
| 23 |
 |
Defcon 19 - Packetfence, The Open Source Nac: What We've Done In The Last |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
8159 |
None |
| 24 |
 |
Defcon 19- Federation And Empire |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6863 |
None |
| 25 |
 |
Defcon 19 - Three Generations Of Dos Attacks (With Audience Participation, As Victims) |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
8756 |
1 |
| 26 |
 |
Defcon 19 - Building The Def Con Network, Making A Sandbox For 10,000 Hackers |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6627 |
None |
| 27 |
 |
Defcon 19 - Kinectasploit: Metasploit Meets Kinect |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7694 |
None |
| 28 |
 |
Defcon 19 - Physical Memory Forensics For Cache |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6206 |
None |
| 29 |
 |
Defcon 19 - Metasploit Vsploit Modules |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7514 |
None |
| 30 |
 |
Defcon 19 - Strategic Cyber Security: An Evaluation Of Nation-State Cyber Attack |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6821 |
None |
| 31 |
 |
Defcon 19 - Getting F***** On The River |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7000 |
None |
| 32 |
 |
Defcon 19 - Real World Web Services Testing For Web Hackers |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
10872 |
None |
| 33 |
 |
Defcon 19 - Upnp Mapping |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7283 |
None |
| 34 |
 |
Defcon 19 - Get Off Of My Cloud ,Cloud Credential Compro |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6426 |
None |
| 35 |
 |
Defcon 19: Eric Fulton - Cellular Privacy: A Forensic Analysis Of Android Network Traffic |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6987 |
None |
| 36 |
 |
Defcon 19 - Mamma's Don't Let Your Babies Grow Up To Be Pen Testers |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7762 |
None |
| 37 |
 |
Defcon 19 - Gone In 60 Minutes: Stealing Sensitive Data From Thousands Of Systems Simultaneously With Opendlp |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7002 |
None |
| 38 |
 |
Defcon 19 - Steganography And Cryptography 101 |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7118 |
None |
| 39 |
 |
Defcon 19: Foofus - Handicapping The Us Supreme Court: Can We Get Rich By Forceful Browsing? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6091 |
None |
| 40 |
 |
Defcon 19: Panel - Pci 2.0: Still Compromising Controls And Compromising Security |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6419 |
None |
| 41 |
 |
Defcon 19 - Duckwall - A Bridge Too Far: Defeating Wired 802.1x With A Tran |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7592 |
None |
| 42 |
 |
Defcon 19: Whitfield Diffie And Moxie Marlinspike |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6696 |
None |
| 43 |
 |
Defcon 19: Dark Tangent, Rod Beckstrom, Jerry Dixon, Tony Sager, Linton Wells Ii - Former Keynot |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6418 |
None |
| 44 |
 |
Defcon 19: Nelson Elhage - Virtualization Under Attack: Breaking Out Of Kvm |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6874 |
None |
| 45 |
 |
Defcon 19: Datagram - Introduction To Tamper Evident Devices |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6657 |
None |
| 46 |
 |
Defcon 19 - All Your Voice Are Belong To Us |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7116 |
None |
| 47 |
 |
Defcon 19 - I Am Not A Doctor But I Play One On Your Network |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6656 |
None |
| 48 |
 |
Defcon 19 - Bit-Squatting: Dns Hijacking Without Exploitation |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
8044 |
None |
| 49 |
 |
Defcon 19 - Safe To Armed In Seconds: A Study Of Epic Fails Of Popular Gun Safes |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7091 |
None |
| 50 |
 |
Defcon 19 - Lives On The Line: Securing Crisis Maps In Libya, Sudan, And Pakist |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6346 |
None |
| 51 |
 |
Defcon 19 - Cipherspaces/Darknets: An Overview Of Attack S |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7210 |
None |
| 52 |
 |
Defcon 19 - Speaking With Cryptographic Oracles |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6339 |
None |
| 53 |
 |
Defcon 19 - Abusing Html5 |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6794 |
None |
| 54 |
 |
Defcon 19 - Taking Your Ball And Going Home; Building Your Own Secure Storage Space |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6600 |
None |
| 55 |
 |
Defcon 19 - Internet Kiosk Terminals : The Redux |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7135 |
None |
| 56 |
 |
Defcon 19 - The Art And Science Of Security Research |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6762 |
1 |
| 57 |
 |
Defcon 19 - Operational Use Of Offensive Cyber |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7231 |
None |
| 58 |
 |
Defcon 19 - Kernel Exploitation Via Uninitialized Stack |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7093 |
None |
| 59 |
 |
Defcon 19 - Bulletproofing The Cloud: Are We Any Closer To Security? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6072 |
None |
| 60 |
 |
Defcon 19 - Smile For The Grenade! |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5375 |
None |
| 61 |
 |
Defcon 19 - The History And Evolution Of Computer Viruses |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7234 |
None |
| 62 |
 |
Defcon 19: Panel - Represent! Defcon Groups, Hackerspaces, And You. |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5537 |
None |
| 63 |
 |
Defcon 19: Panel- Smartfuzzing The Web: Carpe Vestra Foramina |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5492 |
None |
| 64 |
 |
Defcon 19 - Earth Vs. The Giant Spider: Amazingly True |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5474 |
None |
| 65 |
 |
Defcon 19 - From Printer To Pwnd: Leveraging Multifunction Printers During Penetr |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6769 |
None |
| 66 |
 |
Defcon 19 -Assessing Civilian Willingness To Participate In On-Line |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5620 |
None |
| 67 |
 |
Defcon 19 - An Insider Look At International Cyber Security Threats And Tren |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5770 |
None |
| 68 |
 |
Defcon 19: Hubris And A5h3r4h - Anonymous Cyber War |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5645 |
None |
| 69 |
 |
Defcon 19 -Economics Of Password Cracking In The Gpu Era |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6115 |
None |
| 70 |
 |
Defcon 19 - Linux Thread Injection Kit |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7236 |
None |
| 71 |
 |
Defcon 19 - The Art Of Trolling |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
23035 |
None |
| 72 |
 |
Defcon 19 - Black Ops Of Tcp/Ip 2011 |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5755 |
None |
| 73 |
 |
Defcon 19: Dave Kennedy (Rel1k) - Hacking Your Victims Over Power Lines |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6592 |
None |
| 74 |
 |
Defcon 19 - How Our Browsing History Is Leaking Into The Cloud |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
7065 |
None |
| 75 |
 |
Defcon 19 - Hacking And Securing Db2 Luw Databases |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5840 |
None |
| 76 |
 |
Defcon 19 - Sounds Like Botnet |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6241 |
None |
| 77 |
 |
Defcon 19 - Dcflux In: License To Transmit |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5537 |
None |
| 78 |
 |
Defcon 19 - Balancing The Pwn Trade Deficit -- Apt Secrets In Asia |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6197 |
None |
| 79 |
 |
Defcon 19 - How I Lost My Eye: Exp |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5250 |
None |
| 80 |
 |
Defcon 19: Grayson Lenik - I'M Your Mac(B)Daddy |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5668 |
None |
| 81 |
 |
Defcon 19: Ryan Linn - Pig: Finding Truffles Without Leaving A Trace |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5899 |
None |
| 82 |
 |
Defcon 19: David Litchfield - Hacking And Forensicating An Oracle Database Server |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6148 |
None |
| 83 |
 |
Defcon 19: William Manning - Pervasive Cloaking |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5399 |
None |
| 84 |
 |
Defcon 19: Joey Maresca - We're (The Government) Here To Help: A Look At How Fips 140 |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5378 |
None |
| 85 |
 |
Defcon 19: Moxie Marlinspike - Ssl And The Future Of Authenticity |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5796 |
None |
| 86 |
 |
Defcon 19: Jon Mccoy - Hacking .Net Applications: The Black Arts |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6741 |
None |
| 87 |
 |
Defcon 19: Wesley Mcgrew - Covert Post-Exploitation Forensics With Metasploit |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
6481 |
None |
| 88 |
 |
Defcon 19: John Mcnabb - Vulnerabilities Of Wireless Water Meter Networks |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 19, Defcon 19, dc-19 |
5659 |
None |
| 89 |
 |
Defcon - 18 Foca2: The Foca Strikes Back |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
6325 |
1 |
| 90 |
 |
Defcon 18 - Connection String Parameter Attacks |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5682 |
None |
| 91 |
 |
Defcon 18 - Wpa Too! |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5987 |
None |
| 92 |
 |
Defcon 18 - Evilgrade, You Still Have Pending Upgrades? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5759 |
None |
| 93 |
 |
Defcon 18 - Cyber[Crime | War] Charting Dangerous Waters |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5568 |
None |
| 94 |
 |
Defcon 18 - Scada And Ics For Security Experts: How To Avoid Cyberdouchery |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5522 |
None |
| 95 |
 |
Defcon 18 - Exploitation On Arm - Technique And Bypassing Defense Mechanisms |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5899 |
None |
| 96 |
 |
Defcon 18 - Web Services We Just Don't Need |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5478 |
None |
| 97 |
 |
Defcon 18 - Mobile Privacy: Tor On The Iphone And Other Unusual Devices |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5489 |
None |
| 98 |
 |
Defcon 18 - Who Cares About Ipv6? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5547 |
None |
| 99 |
 |
Defcon 18 - Seccubus . Analyzing Vulnerability Assessment Data The Easy Way... |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5895 |
None |
| 100 |
 |
Defcon 18 - Massexploitation |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5554 |
None |
| 101 |
 |
Defcon 18 - Resilient Botnet Command And Control With Tor |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5589 |
None |
| 102 |
 |
Defcon 18 - How Hackers Won The Zombie Apocalypse |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5548 |
None |
| 103 |
 |
Defcon 18 - Exploiting Scada Systems |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5818 |
None |
| 104 |
 |
Defcon 18 - Cloud Computing, A Weapon Of Mass Destruction? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5741 |
None |
| 105 |
 |
Defcon 18 - Google Toolbar: The Narc Within |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5411 |
None |
| 106 |
 |
Defcon 18 - Open Public Sensors And Trend Monitoring |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5416 |
None |
| 107 |
 |
Defcon 18 - Bad Memories |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4964 |
None |
| 108 |
 |
Defcon 18 - Kartograph : Finding A Needle In A Haystack Or How To Apply Reverse Engineering Techniques To Cheat At Video Games |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5609 |
None |
| 109 |
 |
Defcon 18 - Token Kidnapping's Revenge |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5480 |
None |
| 110 |
 |
Defcon 18 - Hacking Facebook Privacy |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5775 |
None |
| 111 |
 |
Defcon 18 - Our Instrumented Lives: Sensors, Sensors, Everywhere... |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5233 |
None |
| 112 |
 |
Defcon 18 - Programmable Hid Usb Keystroke Dongle: Using The Teensy As A Pen Testing Device |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
6147 |
None |
| 113 |
 |
Defcon 18 - Ipv6: No Longer Optional |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5444 |
None |
| 114 |
 |
Defcon 18 - Function Hooking For Mac Osx And Linux |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
6275 |
None |
| 115 |
 |
Defcon 18 - Exploiting Internet Surveillance Systems |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5356 |
None |
| 116 |
 |
Defcon 18 - Physical Security : You're Doing It Wrong! |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5457 |
None |
| 117 |
 |
Defcon 18 - The Search For Perfect Handcuffs... And The Perfect Handcuff Key |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5020 |
None |
| 118 |
 |
Defcon 18 - Katana: Portable Multi-Boot Security Suite |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
6099 |
None |
| 119 |
 |
Defcon 18 - Breaking Bluetooth By Being Bored |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
6442 |
None |
| 120 |
 |
Defcon 18 - An Observatory For The Ssliverse |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5076 |
None |
| 121 |
 |
Defcon 18 - How Unique Is Your Browser? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5410 |
None |
| 122 |
 |
Defcon 18 - Your Boss Is A Douchebag... How About You? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5525 |
None |
| 123 |
 |
Defcon 18 - Hacking With Hardware: Introducing The Universal Rf Usb Keyboard Emulation Device - Urfuked |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5938 |
None |
| 124 |
 |
Defcon 18 - Be A Mentor! |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5416 |
None |
| 125 |
 |
Defcon 18 - Hacking And Protecting Oracle Database Vault |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5795 |
None |
| 126 |
 |
Defcon 18 - Trolling Reverse-Engineers With Math: Ness... It Hurts... |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5556 |
1 |
| 127 |
 |
Defcon 18 - The Anatomy Of Drug Testing |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5429 |
None |
| 128 |
 |
Defcon 18 - Mastering The Nmap Scripting Engine |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5918 |
None |
| 129 |
 |
Defcon 18 - Live Fire Exercise: Baltic Cyber Shield 2010 |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5615 |
None |
| 130 |
 |
Defcon 18 - Making The Def Con 18 Badge |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5565 |
None |
| 131 |
 |
Defcon 18 - Legal Developments In Hardware Hacking |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5318 |
None |
| 132 |
 |
Defcon 18 - The Law Of Laptop Search And Seizure |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5191 |
None |
| 133 |
 |
Defcon 18 - Tales From The Crypto |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5659 |
None |
| 134 |
 |
Defcon 18 - Constricting The Web: Offensive Python For Web Hackers |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5798 |
None |
| 135 |
 |
Defcon 18 - How To Hack Millions Of Routers |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
11639 |
None |
| 136 |
 |
Defcon 18 - Ripping Media Off Of The Wire |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5696 |
None |
| 137 |
 |
Defcon 18 - Foe‚ The Release Of Feed Over Email, A Solution To Feed Controversial News To Censored Countries |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5189 |
None |
| 138 |
 |
Defcon 18 - How To Get Your Fbi File (And Other Information You Want From The Federal Government) |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5258 |
None |
| 139 |
 |
Defcon 18 - Physical Computing, Virtual Security: Adding The Arduino Microcontroller Development Environment To Your Security Toolbox |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4952 |
None |
| 140 |
 |
Defcon 18 - Decoding Recaptcha |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5300 |
None |
| 141 |
 |
Defcon 18 - Nosql == No Sql Injections? |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5071 |
None |
| 142 |
 |
Defcon 18 - Drivesploit: Circumventing Both Automated And Manual Drive-By-Download Detection |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5052 |
None |
| 143 |
 |
Defcon 18 - 0box Analyzer: Afterdark Runtime Forensics For Automated Malware Analysis And Clustering |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4878 |
None |
| 144 |
 |
Defcon 18 - Exploiting Digital Cameras |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5301 |
1 |
| 145 |
 |
Defcon 18 - Jackpotting Automated Teller Machines Redux |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
5276 |
None |
| 146 |
 |
Defcon 18 - Black Ops Of Fundamental Defense: Web Edition |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4482 |
None |
| 147 |
 |
Defcon 18 - How I Met Your Girlfriend |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
6579 |
None |
| 148 |
 |
Defcon 18 - Powershell...Omfg |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4963 |
1 |
| 149 |
 |
Defcon 18 - Perspectives On Cyber Security And Cyber Warfare |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4345 |
None |
| 150 |
 |
Defcon 18 - Malware Migrating To Gaming Consoles: Embedded Devices, An Antivirus-Free Safe Hideout For Malware |
12 years, 4 months |
Securitytube_Poster |
securitytube, defcon, def con, hacking, hackers, information security, convention, computer security, DC 18, defcon-18, dc-18 |
4735 |
None |